Essential Guide: 5 Powerful Ways To Master Parental Controls
Essential Guide: 5 Powerful Ways to Master Parental Controls
Related Articles: Essential Guide: 5 Powerful Ways to Master Parental Controls
- Effortless 5-Step Guide To Building Your Ultimate Gaming PC
- Effortlessly Recover 3 Crucial Lost Files From Any Device
- Secure Your Future: 5 Crucial Steps To Ultimate Data Backup
- Conquer 5 Crucial Cloud Storage Challenges For Ultimate Efficiency
- Amazing Battery Life! 7 Power Tips For Smartphone Optimization
Introduction
With great pleasure, we will explore the intriguing topic related to Essential Guide: 5 Powerful Ways to Master Parental Controls. Let’s weave interesting information and offer fresh perspectives to the readers.
Table of Content
Essential Guide: 5 Powerful Ways to Master Parental Controls
Protecting your children online is a crucial responsibility in today’s digital age. The internet offers incredible opportunities for learning and connection, but it also exposes children to potential dangers, including inappropriate content, cyberbullying, and online predators. Setting up robust parental controls is no longer a luxury; it’s a necessity. This comprehensive guide will walk you through five powerful methods to safeguard your children’s online experience across various devices, empowering you to create a safer digital environment for your family.
1. Leveraging Operating System Built-in Controls:
Both Apple’s iOS (for iPhones and iPads) and Google’s Android (for Android phones and tablets) offer robust built-in parental control features. These are often the easiest starting point, providing a solid foundation for online safety. Let’s explore the key features and how to utilize them effectively:
-
Screen Time (iOS): This powerful tool allows you to set daily limits for app usage, schedule downtime, and even block specific apps during certain hours. You can create separate profiles for each child, customizing limits and restrictions based on their age and needs. The "Downtime" feature is particularly useful for enforcing "no screen time" periods before bed or during family time. You can also use the "Always Allowed" feature to exempt essential apps like communication apps from downtime.
-
Google Family Link (Android): Google Family Link is a dedicated app designed for parental control on Android devices. It allows you to manage app downloads and purchases, monitor app usage, locate your child’s device, and set digital wellbeing limits. You can also remotely lock or unlock the device, a crucial feature in emergency situations. The app provides detailed reports on your child’s activity, allowing you to monitor their online behavior and intervene if necessary. Family Link works best when paired with Google’s other services, providing a more comprehensive safety net.
-
Content Filtering: Both iOS and Android offer some level of content filtering, although the effectiveness varies. You can typically restrict access to explicit content, mature themes, and age-inappropriate apps. While these built-in filters are a good starting point, they may not be sufficient to block all potentially harmful content. This is where third-party apps and services come into play.
Understanding the Limitations: While built-in controls are convenient and readily available, they have limitations. They may not cover all aspects of online safety, such as social media usage and online gaming. Furthermore, tech-savvy children may find ways to circumvent these controls. Therefore, it’s crucial to combine these built-in features with other parental control methods for comprehensive protection.
2. Employing Third-Party Parental Control Apps:
Numerous third-party apps provide more advanced parental control features than those built into operating systems. These apps often offer features like website blocking, app usage monitoring, location tracking, and even social media monitoring. Choosing the right app depends on your specific needs and budget. Some popular options include:
-
Qustodio: Qustodio offers comprehensive parental controls across multiple devices (computers, smartphones, tablets). It allows you to monitor app usage, block inappropriate websites, filter content, and track location. It also provides detailed reports on your child’s online activity.
-
Bark: Bark focuses on monitoring social media and messaging apps for signs of cyberbullying, self-harm, or other risky behaviors. It analyzes text messages, emails, and social media posts for potential red flags and alerts parents to potential issues.
-
Net Nanny: Net Nanny is a long-standing parental control solution that offers web filtering, app blocking, and time management features. It’s known for its strong content filtering capabilities and its ability to block access to inappropriate websites and content.
-
Norton Family: Norton Family provides comprehensive protection across various devices, including web filtering, app control, location tracking, and online activity monitoring. It is integrated with other Norton security products, providing a holistic approach to online safety.
Choosing the Right App: When selecting a third-party app, consider factors such as the range of devices it supports, the level of control it offers, its ease of use, and its cost. Read reviews and compare features before making a decision. Remember that no app is foolproof, and it’s essential to combine app-based controls with open communication and education.
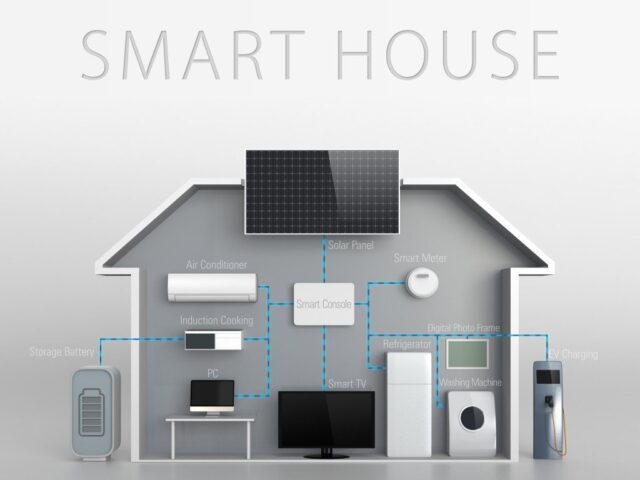
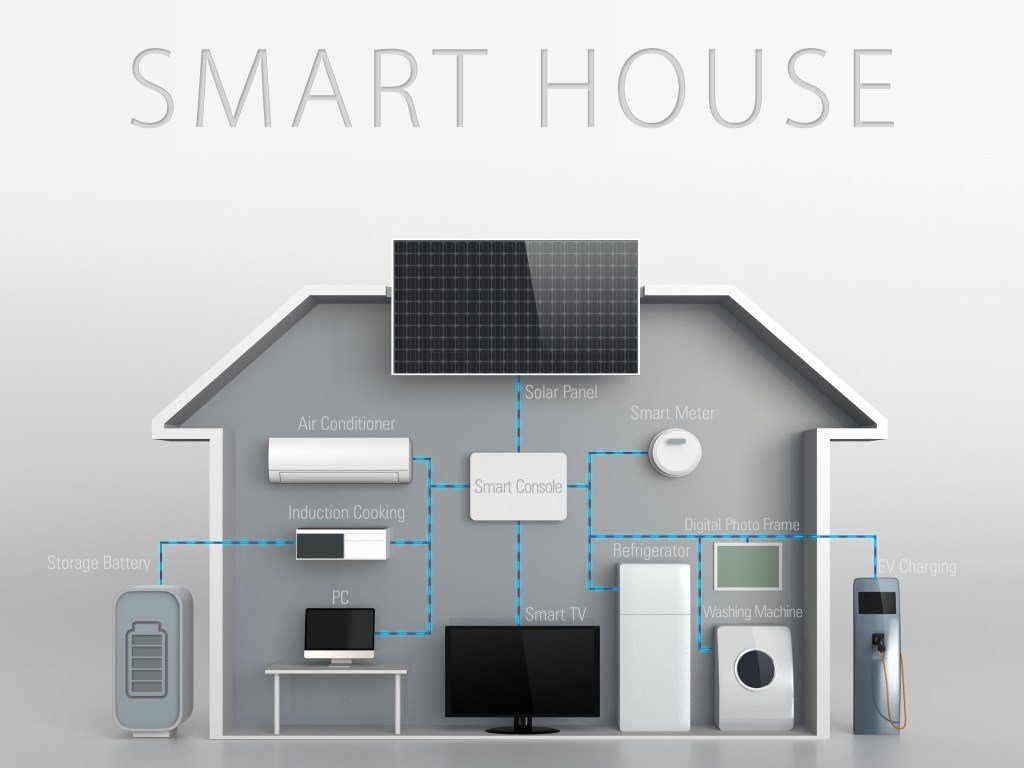
3. Utilizing Router-Based Parental Controls:
Many modern routers offer built-in parental control features. These controls work at the network level, meaning they can filter content and restrict access for all devices connected to your home Wi-Fi network. This is particularly useful for devices that may not have operating system-level parental controls, such as smart TVs or game consoles.
Features typically included in router-based parental controls include:
-
Website Blocking: You can create a list of websites to block, preventing access to inappropriate or harmful content.
-
Time Scheduling: You can schedule internet access, allowing internet access only during specific times of the day.
-
Content Filtering: Some routers offer content filtering based on age ratings or keywords.
-
Device Management: You can manage the devices connected to your network and restrict access for specific devices.
Setting up router-based controls: The process varies depending on your router model. Consult your router’s manual for instructions on how to access and configure the parental control settings. This method is an effective layer of protection, but it may not be sufficient on its own.
4. Open Communication and Education:
Technology is constantly evolving, and parental controls alone are not a complete solution. Open communication and education are essential components of online safety. Talk to your children about online safety, explain the potential risks, and teach them how to navigate the internet responsibly.
-
Discuss online dangers: Explain the risks of cyberbullying, online predators, and inappropriate content.
-
Establish clear rules: Set clear rules for online behavior and internet usage.
-
Teach critical thinking: Encourage your children to think critically about the information they encounter online and to be cautious about sharing personal information.
-
Promote responsible social media use: Teach your children how to use social media safely and responsibly.
-
Encourage open communication: Create a safe space where your children feel comfortable talking to you about their online experiences and any concerns they may have.
5. Regularly Review and Update Controls:
Parental controls are not a "set it and forget it" solution. Regularly review and update your controls to ensure they are still effective and appropriate for your children’s age and maturity level. As your children grow older, their needs and online activities will change, requiring adjustments to your parental control strategies. Technology also evolves rapidly, so keeping your software updated and exploring new parental control features is crucial.
-
Check for updates: Regularly update your parental control apps and your router’s firmware to benefit from the latest security features and bug fixes.
-
Review activity logs: Periodically review the activity logs provided by your parental control apps or router to monitor your children’s online activities and identify any potential issues.
-
Adapt to changing needs: As your children grow older, adjust your parental control settings to reflect their increasing maturity and independence.
-
Stay informed: Stay updated on the latest online threats and trends to better protect your children.
In conclusion, creating a safe online environment for your children requires a multi-faceted approach. Combining operating system features, third-party apps, router controls, open communication, and regular review will provide a robust and adaptable parental control system. Remember, the goal is not to restrict your children’s access to the internet entirely, but to equip them with the knowledge and tools to navigate the digital world safely and responsibly. By implementing these five powerful strategies, you can empower your children to explore the internet’s boundless opportunities while minimizing the risks.
Closure
Thus, we hope this article has provided valuable insights into Essential Guide: 5 Powerful Ways to Master Parental Controls. We thank you for taking the time to read this article. See you in our next article!
google.com