Conquer 5 Frustrating Wi-Fi Problems: Ultimate Troubleshooting Guide
Conquer 5 Frustrating Wi-Fi Problems: Ultimate Troubleshooting Guide
Related Articles: Conquer 5 Frustrating Wi-Fi Problems: Ultimate Troubleshooting Guide
- Effortless 5-Step Guide To Building Your Ultimate Gaming PC
- Effortless Smart Home Setup: 5 Essential Steps To Automation Bliss
- Ultimate Guide: 7 Powerful Steps To Secure Your Digital Fortress
Introduction
In this auspicious occasion, we are delighted to delve into the intriguing topic related to Conquer 5 Frustrating Wi-Fi Problems: Ultimate Troubleshooting Guide. Let’s weave interesting information and offer fresh perspectives to the readers.
Table of Content
Conquer 5 Frustrating Wi-Fi Problems: Ultimate Troubleshooting Guide
Wi-Fi woes are a universal experience. That frustrating moment when your internet connection sputters, lags, or completely vanishes can derail productivity and leisure alike. But before you throw your router across the room (we don’t recommend it!), take a deep breath. This comprehensive guide will equip you with the knowledge and steps to diagnose and resolve 5 common Wi-Fi problems, transforming your digital frustration into triumphant connectivity.
Problem 1: Slow or Intermittent Connection
A slow or intermittent connection is perhaps the most common Wi-Fi complaint. The feeling of watching your loading bar crawl at a snail’s pace is enough to drive anyone mad. Here’s a methodical approach to troubleshooting this issue:
-
Check Your Internet Speed: The first step is to determine if the problem lies with your Wi-Fi network itself or your internet service provider (ISP). Use a speed test website (like Ookla’s Speedtest.net) to measure your download and upload speeds. Compare these results to the speed you’re paying for. If your speeds are significantly slower, contact your ISP.
-
Identify Interference: Wi-Fi signals can be disrupted by various sources of interference, including:
- Other Wireless Devices: Overlapping Wi-Fi networks from neighbors, microwaves (operating on the 2.4 GHz frequency), cordless phones, and even Bluetooth devices can cause interference. Try changing your Wi-Fi channel (more on this below).
- Physical Obstacles: Walls, furniture, and even large appliances can weaken your Wi-Fi signal. Try moving your router to a more central location in your home, away from obstructions.
- Distance from Router: The further you are from your router, the weaker the signal will become. Consider using a Wi-Fi extender or mesh network to improve coverage in areas with weak signals.
-
Check Your Router’s Location: As mentioned, the placement of your router is crucial. Avoid placing it near metallic objects, large appliances, or in corners where the signal can be trapped. Ideally, it should be elevated and centrally located.
-
Restart Your Router and Modem: Sometimes, a simple reboot can resolve temporary glitches. Unplug both your router and modem from the power outlet, wait 30 seconds, and then plug them back in, starting with the modem.
-
Update Your Router’s Firmware: Outdated firmware can contain bugs that affect performance. Check your router manufacturer’s website for firmware updates and follow their instructions to update your router’s software.
-
Change Your Wi-Fi Channel: Wi-Fi networks operate on different channels. If your channel is crowded with other networks, it can lead to slowdowns. Use a Wi-Fi analyzer app (available for smartphones and computers) to identify less congested channels and change your router’s settings accordingly.
-
Check for Malware or Viruses: Malware on your devices can consume bandwidth and slow down your internet connection. Run a full scan with your antivirus software.
Problem 2: Dropped Connections
Constantly dropping connections can be incredibly frustrating. Here’s how to tackle this issue:
-
Check for Driver Issues: Outdated or corrupted Wi-Fi drivers on your devices can lead to dropped connections. Update your drivers through your device’s manufacturer’s website or your operating system’s update manager.
-
Examine Router Logs: Many routers have built-in logging capabilities. Check these logs for any error messages or indications of connection problems.
-
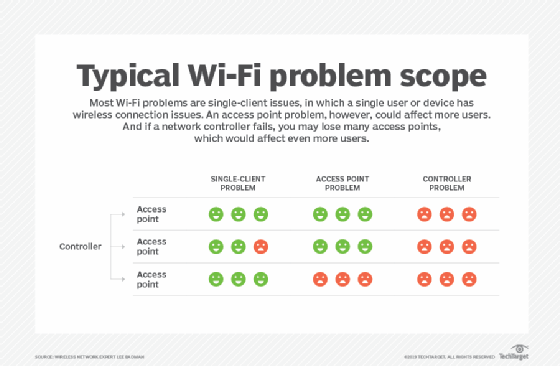
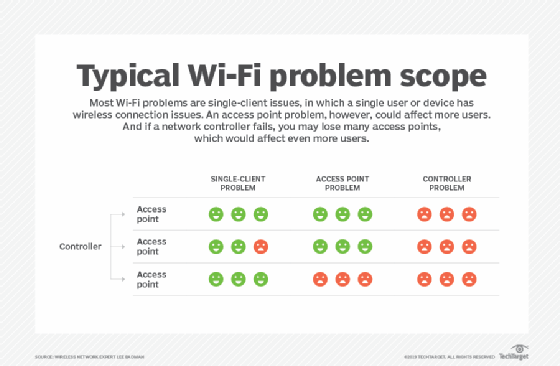
Assess Router Capacity: If you have many devices connected to your Wi-Fi network simultaneously, it may be overloaded, leading to dropped connections. Consider upgrading to a router with a higher capacity or implementing a mesh network.
-
Power Cycle Your Devices: Sometimes, a simple power cycle of both your router and your devices can resolve temporary glitches.
-
Check for Hardware Problems: A faulty router or modem can cause dropped connections. Try replacing them if you suspect hardware issues. Inspect cables for damage or loose connections.
-
Investigate Network Congestion: If you’re experiencing frequent drops during peak usage times, it could indicate network congestion. Consider upgrading your internet plan or optimizing your network settings.
Problem 3: Limited Range
A limited Wi-Fi range means dead zones in your home where you can’t access the internet. Here are solutions:
-
Wi-Fi Extenders: These devices boost your Wi-Fi signal, extending its reach to areas with weak coverage.
-
Mesh Networks: Mesh networks consist of multiple interconnected nodes that create a seamless Wi-Fi coverage area throughout your home.
-
Powerline Adapters: These adapters use your home’s electrical wiring to transmit data, extending your Wi-Fi network to areas where a wireless signal is weak.
-
Optimal Router Placement: As mentioned earlier, carefully consider the placement of your router to minimize signal obstructions.
Problem 4: Security Issues
Security breaches can be disastrous. Here’s how to protect your network:
-
Strong Password: Use a strong, unique password for your Wi-Fi network. Avoid easily guessable passwords and use a password manager to generate and store complex passwords.
-
WPA2/WPA3 Encryption: Ensure your router is using WPA2 or WPA3 encryption to protect your network from unauthorized access.
-
Regular Firmware Updates: Keeping your router’s firmware updated is crucial for patching security vulnerabilities.
-
Firewall: Enable your router’s firewall to block unauthorized access attempts.
-
MAC Address Filtering: This feature allows you to restrict access to your Wi-Fi network to only specific devices.
Problem 5: Unable to Connect
This issue prevents you from accessing the internet altogether. Here’s a systematic approach:
-
Verify Network Name and Password: Double-check that you’re entering the correct network name (SSID) and password.
-
Check Router Status Lights: Examine the lights on your router and modem. If any lights are flashing erratically or not illuminated at all, it could indicate a hardware problem.
-
Check Device Settings: Ensure your device is configured to connect to the correct Wi-Fi network.
-
Forget and Reconnect: On your device, "forget" your Wi-Fi network and then try reconnecting.
-
Contact Your ISP: If you’ve tried all the above steps and still can’t connect, contact your internet service provider to troubleshoot the problem on their end. They might have an outage or a problem with your account.
By systematically following these troubleshooting steps, you can effectively diagnose and resolve many common Wi-Fi problems. Remember to be patient and methodical, and don’t hesitate to seek professional help if you’re still struggling. With a little perseverance, you can conquer your Wi-Fi woes and enjoy a smooth, reliable internet connection.
Closure
Thus, we hope this article has provided valuable insights into Conquer 5 Frustrating Wi-Fi Problems: Ultimate Troubleshooting Guide. We thank you for taking the time to read this article. See you in our next article!
google.com