Revolutionary Leap: 5 Crucial Steps For Autonomous Car Domination
Revolutionary Leap: 5 Crucial Steps for Autonomous Car Domination
Related Articles: Revolutionary Leap: 5 Crucial Steps for Autonomous Car Domination
- Amazing Breakthroughs: 5 Revolutionary AI Innovations Reshaping Our World
- Amazing Breakthroughs: 5 Revolutionary Green Tech Solutions Transforming Our Planet
- Revolutionary AI Innovations
- Revolutionary 5G’s Impact: The Exploding Power Of Edge Computing
- Transformative Wearable Tech
Introduction
With enthusiasm, let’s navigate through the intriguing topic related to Revolutionary Leap: 5 Crucial Steps for Autonomous Car Domination. Let’s weave interesting information and offer fresh perspectives to the readers.
Table of Content
Revolutionary Leap: 5 Crucial Steps for Autonomous Car Domination
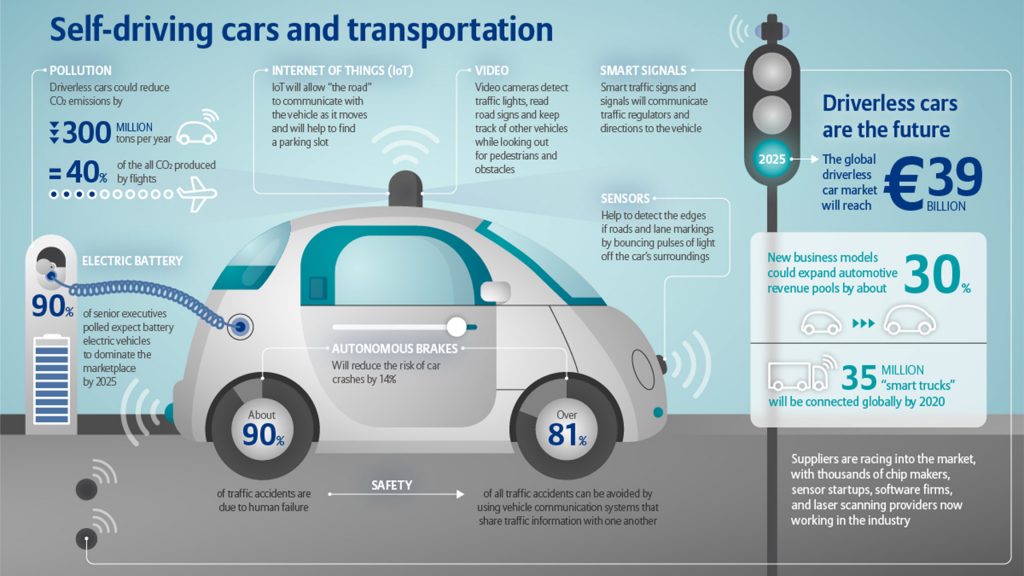
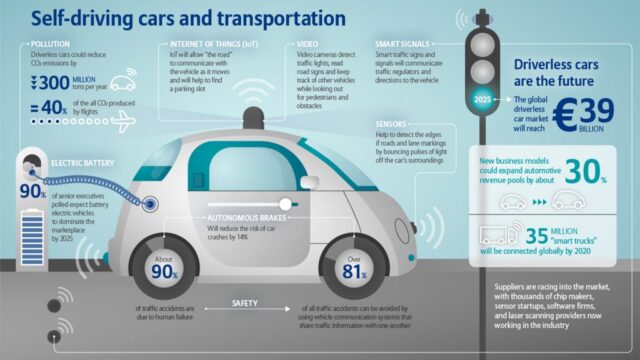
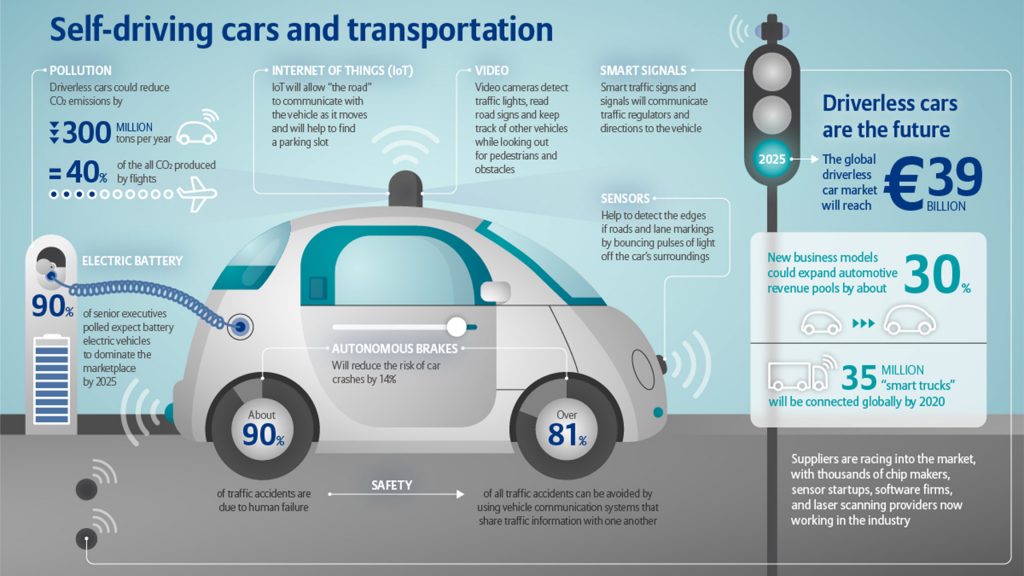
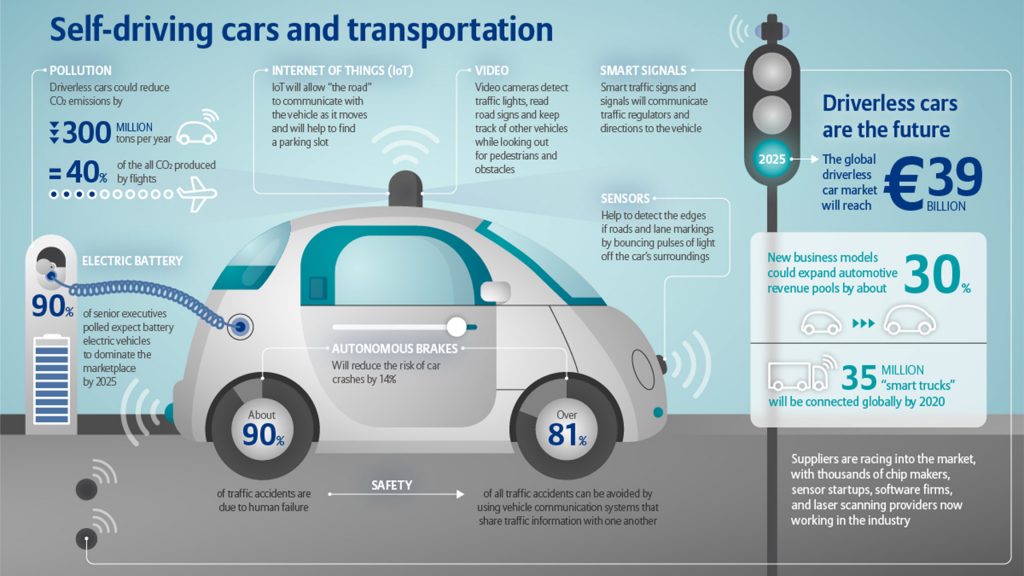
The autonomous vehicle revolution is no longer a distant dream; it’s hurtling towards us at breakneck speed. While fully autonomous cars aren’t yet ubiquitous on our roads, the advancements made in recent years are nothing short of astonishing. From sophisticated sensor technologies to groundbreaking artificial intelligence, the components needed for a truly driverless future are rapidly maturing. But the road ahead isn’t without its potholes. This article will delve into five crucial steps necessary to achieve widespread adoption and true dominance of the autonomous vehicle market, highlighting the challenges and opportunities that lie ahead.
1. Conquering the "Edge Cases": Addressing Unpredictability on the Road
One of the biggest hurdles to widespread autonomous vehicle adoption remains the unpredictability of human behavior and real-world scenarios. While autonomous systems excel in controlled environments, navigating the chaotic reality of human drivers, unpredictable pedestrians, and unexpected events like sudden weather changes or road construction poses a significant challenge. These are what engineers refer to as "edge cases"—situations outside the parameters of typical programming and testing.
Current autonomous driving systems rely heavily on sensor fusion, combining data from cameras, lidar, radar, and ultrasonic sensors to create a 360-degree view of the vehicle’s surroundings. However, even with this advanced technology, interpreting complex scenarios involving multiple interacting agents (cars, pedestrians, cyclists) remains a significant computational burden. For example, predicting the actions of a pedestrian who suddenly darts into the street against a red light requires a level of cognitive understanding and anticipation that current AI systems are still struggling to master.
The solution lies in a combination of enhanced sensor technology, more robust machine learning algorithms, and the development of sophisticated simulation environments for testing. Next-generation lidar systems with increased range and resolution are crucial for better object detection and classification, particularly in low-light conditions. Simultaneously, advancements in deep learning are paving the way for AI systems that can better understand context and predict the likely behavior of other road users. Creating realistic and diverse simulation environments is also critical for training autonomous vehicles to handle a wider range of edge cases before they are deployed on public roads. This requires generating vast amounts of synthetic data that accurately reflects the variability and complexity of real-world driving conditions. The ability to seamlessly integrate data from real-world driving experiences with synthetic data is key to achieving a robust and reliable system.
2. Building Trust: Addressing Public Perception and Safety Concerns
Public perception plays a crucial role in the success of autonomous vehicles. Despite the potential benefits, many people remain hesitant to trust a machine with their lives. Concerns about safety, security, and ethical considerations are widespread and need to be addressed head-on. High-profile accidents involving autonomous vehicles, however rare, have fueled public apprehension and eroded confidence.
To build trust, transparency is paramount. Companies developing autonomous driving technology need to be open and honest about the limitations of their systems and the ongoing challenges they face. Clearly communicating the safety measures implemented, including redundancy systems and fail-safe mechanisms, is essential. Furthermore, rigorous independent testing and verification are crucial to demonstrate the safety and reliability of autonomous vehicles to the public. The development of standardized safety protocols and regulations is also necessary to ensure a consistent level of safety across different manufacturers.
Beyond safety, ethical considerations surrounding accident avoidance and decision-making need to be carefully addressed. For example, how should an autonomous vehicle make a decision in a unavoidable accident scenario where it must choose between harming its passengers or pedestrians? Developing clear ethical guidelines and algorithms that reflect societal values is crucial for building public trust and acceptance. Open discussions involving ethicists, policymakers, and engineers are essential to navigate these complex moral dilemmas.
3. Infrastructure Integration: Paving the Way for Seamless Operation
The widespread adoption of autonomous vehicles will require significant upgrades to existing road infrastructure. While autonomous cars can navigate existing roads, dedicated infrastructure can significantly enhance their performance and safety. Smart traffic management systems that communicate with autonomous vehicles can optimize traffic flow, reduce congestion, and improve safety. This includes intelligent traffic signals that provide real-time information to autonomous vehicles, allowing them to anticipate changes in traffic conditions and adjust their driving accordingly.
The implementation of Vehicle-to-Everything (V2X) communication technology is also crucial. V2X allows autonomous vehicles to communicate with other vehicles, infrastructure, and pedestrians, enabling a more coordinated and efficient traffic flow. This can reduce the likelihood of accidents by providing early warnings of potential hazards and allowing vehicles to react more effectively to unforeseen circumstances. For example, V2X can alert an autonomous vehicle to an approaching emergency vehicle or a sudden road closure, allowing it to take evasive action.
The development of dedicated autonomous vehicle lanes or roadways could also improve safety and efficiency. These lanes could be designed to optimize the flow of autonomous vehicles, minimizing the risk of interactions with human-driven vehicles. Furthermore, the integration of sensors and actuators into the road infrastructure could provide autonomous vehicles with even more precise information about their environment. For example, embedded sensors could detect potholes or slippery surfaces, allowing autonomous vehicles to adjust their driving accordingly.
4. Legal and Regulatory Framework: Navigating the Complex Legal Landscape
The development and deployment of autonomous vehicles are inextricably linked to the legal and regulatory framework governing their operation. The absence of clear and consistent regulations creates significant uncertainty for manufacturers and consumers alike. Issues surrounding liability in the event of an accident, data privacy, and intellectual property rights need to be addressed to create a stable and predictable environment for innovation.
Developing a comprehensive legal framework requires international collaboration to ensure consistency and avoid fragmentation. The establishment of standardized safety testing procedures, certification processes, and liability frameworks is crucial to fostering trust and confidence in the technology. Determining who is liable in the event of an accident involving an autonomous vehicle – the manufacturer, the software developer, or the owner – is a particularly complex issue that requires careful consideration. The definition of "driver" in the context of autonomous vehicles also needs to be clarified, along with the responsibilities and liabilities associated with this role.
Data privacy is another crucial aspect that needs to be addressed. Autonomous vehicles generate vast amounts of data about their surroundings and their operation, raising concerns about the privacy of individuals and their data. The development of robust data protection mechanisms and regulations is essential to ensure that this data is handled responsibly and ethically.
5. Economic Viability and Market Penetration: The Business Case for Autonomous Vehicles
Despite the technological advancements, the economic viability of autonomous vehicles remains a significant challenge. The high cost of development, manufacturing, and deployment is a major barrier to widespread adoption. Furthermore, the business models for autonomous vehicles are still evolving, with uncertainty surrounding revenue streams and profitability.
To achieve economic viability, several factors need to be considered. Reducing the cost of manufacturing autonomous vehicles is crucial, as is developing efficient and scalable business models. The integration of autonomous vehicles into existing transportation systems, such as ride-sharing services and public transportation, could unlock significant economic benefits. The potential for reduced traffic congestion, improved fuel efficiency, and reduced accident rates could also contribute to substantial cost savings.
However, the transition to a fully autonomous transportation system will likely be gradual, with different levels of autonomy being adopted at different paces. Initially, we might see a greater adoption of advanced driver-assistance systems (ADAS) that provide partial automation, followed by a gradual increase in the level of autonomy as technology matures and public confidence grows. The development of robust business models that can support this gradual transition is crucial for the long-term success of the autonomous vehicle market. This might involve a combination of different revenue streams, such as subscription fees, pay-per-mile charges, and advertising revenue.
In conclusion, the journey to autonomous vehicle dominance requires a multifaceted approach. Addressing the challenges related to edge cases, building public trust, integrating with infrastructure, establishing a robust legal framework, and ensuring economic viability are all crucial steps. While the road ahead is long and complex, the potential benefits of autonomous vehicles are too significant to ignore. By tackling these challenges head-on, we can pave the way for a safer, more efficient, and more sustainable transportation future.
Closure
Thus, we hope this article has provided valuable insights into Revolutionary Leap: 5 Crucial Steps for Autonomous Car Domination. We thank you for taking the time to read this article. See you in our next article!
google.com